Monday, December 17th, 2018
2018 Review: Data Breaches and Cyber Attacks

2018 Review – Compared to 2017, when WannaCry, Non-Petya and a host of other damaging cyber-attacks occurred, a significant difference can be observed in the severity and number of cyber-attacks that have happened so far in our 2018 review. Although the number of total breaches is lower from our 2018 review (so far) than 2017, the overall trend continues to show more breaches that are impacting tens of millions, if not hundreds of millions, of records at once. Could regulations, such as the EU GDPR have played a major role in this reduction? We hope so! Several companies, irrespective of their size have been paying more attention to the security of their systems and the data within their possession. However, the year did not pass by without its own significant share of major cyber-attacks and disastrous data breaches. We discuss and highlight some of the major cyber-attacks and data breaches that occurred in our 2018 review.
- Crypto Mining: 2018 saw a massive increase in the mining of cryptocurrencies. This process is known as cryptojacking which involves the unauthorised use of a person or organisation’s machine for the mining of cryptocurrency. The Trend Micro midyear round up presented an estimate of an increase in cryptojacking by about 141% in the first quarter of 2018 alone. 90% of cryptojacking activity is done through the use of remote code execution. An example of this was the web script miner discovered on AOL’s platform in April 2018. Cryptojacking usually leads to a fast degradation of a system’s hardware, excessive power consumption and a significant reduction in performance and speed. Crypto mining will still be very much around for a good while.
- Marriott Data Breach: More than 500 million Marriott guests’ information was hacked. Marriott announced the hack on November 30, saying hackers targeted its Starwood reservation system and accessed the personal information of hundreds of millions of guests who have stayed in the hotel chain’s properties since 2014. For roughly 327 million of those guests, the data breach revealed “some combination of name, mailing address, phone number, email address, passport number, Starwood Preferred Guest (‘SPG’) account information, date of birth, gender, arrival and departure information, reservation date, and communication preferences,” according to the company’s statement. Other guests’ credit card numbers and expiration dates also may have been accessed.
- The Aadhaar Data Breach: One of the first major data breaches that occurred in 2018 was the Aadhaar breach were records of all 1.1 billion people in India are suspected to have been breached. A service was being sold by anonymous sellers over WhatsApp that would return private information about any Aadhaar number for some amount of money. The Aadhaar number is a 12-digit unique identification number given to every citizen of India. The data retrieved from this included name, photograph, phone number, home address and email address. For an additional fee, the anonymous sellers could print an ID for any Aadhaar number provided.
- Under Armour : Under Armour’s “My fitness pal” application, an app used to track a user’s diet and exercise was reported to have been breached by hackers in February, 2018. Personal details of about 150 million users are suspected to have been leaked in this breach. The hackers were able to gain access to user email addresses, usernames and hashed passwords. More sensitive information such as user location and credit card details were not reported to have been disclosed in the breach since that data was stored separately. While the passwords were stored as hashes, Under Amour admitted that some part of the encryption had been done with the SHA-1 algorithm which is known to have security flaws and can be broken.
- Facebook:2018 wasn’t particularly a smooth year for Facebook in terms of data breaches. The first came up in March 2018 when reports about Cambridge Analytica gaining access to private information of approximately 50 million Facebook users with the use of a data scrapping app hit the media. By April, 2018 Facebook had sent a notification to about 87 million of their users that their data had been breached. By June 2018, a security researcher Inti De Ceukelaire disclosed another application called Nametest.com had publicly exposed information of over 120 million users. In September, 2018 a vulnerability was discovered that allowed attackers fully take over user accounts. This incident was said to have affected approximately 50 million user accounts. A total of about 90 million accounts were forced to log out by Facebook as a part of the fix. Facebook later disclosed that this might also have affected third party accounts connected to Facebook.
- Dixons Carphone Breach: The Dixon data breach is alleged to have involved 5.9 million payment cards and 10 million personal data records. While the breach occurred in 2017, Dixons Carphone did not discover this breach until June 2018. About 5.8m of the breached card details were chip and pin protected, and no pin codes, card verification values (CVV) or authentication data were accessed, meaning purchases could not be made. However, about 105,000 payment cards from outside the EU and without chip and pin protection were accessed.
- The American Universities Hack: Nine Iranians hackers were arrested for hacking over 300 universities in and out of the United States of America. The hackers were suspected to have stolen about 32 terabytes of data by carrying out multiple carefully crafted spear-phishing attacks targeted at university students and lecturers. The emails tricked the receiver to click a link to steal usernames and passwords. Out of 100,000 targeted accounts, the hackers were able to gain valid credentials to approximately 8000 and 3768 of them were within the United States of America. 144 US universities, 176 universities outside the US, 47 private firms and other organizations like the United Nations were targeted in the attacks.
- Exactis: In June 2018, a data exposure incident occurred in which Exactis; an American marketing company which left approximately 340 million individual data records in a database exposed on a publicly accessible server. While this breach did not involve social security numbers or bank card details, over 2 terabytes of private information about American businesses and individuals were involved including names, addresses, phone numbers and email addresses and quite private information.
- British Airways: For about 2 weeks, hackers were reported to have gained access into British Airways’ systems. According to the management of British Airways, this was carried out by a “sophisticated hacker group of cybercriminals”. Personal and Financial details of customers who made any transactions on their website or mobile application during that period were affected by the breach. Data that was leaked included names, email addresses and credit card details. An approximate of 380,000 transactions were affected in this breach.
- MyHeritage: The DNA testing organisation MyHeritage suffered a major data breach that possibly compromised the email addresses and hashed passwords of about 96 million users. This was discovered after a file named “myheritage” was found by a security researcher on a private server. No DNA data or payment information were leaked.
- The Sacramento Bee Ransom: Two databases belonging to the newspaper Sacramento Bee, a newspaper in California were seized by an attacker in June. The databases involved contained details of Californian voters and also information about subscribers to the newspaper. While a ransom fee was demanded by the attacker in exchange for giving back access, the newspaper deleted the databases instead. The attack exposed an estimate of 53,000 subscribers’ information and personal data of 19.4 million California voters.
What can we learn from the 2018 review on breaches and what lessons can we apply for 2019?
While organisations are actively looking to continuously tighten up their security, 2019 might not be any different in terms of data breaches. We are expecting security spending to grow in response to the rise of attacks. Gartner recently stated that worldwide security spending will rise to $114 billion in 2018, and will increase another 9 percent next year to reach a staggering $124 billion. Similarly, with the rise in connected devices, IoT security will drive more regulations and data protection bills. Data governance will also become a top priority for companies. In the next few years, enterprises will generate more data than they ever have before making data classification and data governance tools a security need. Disruptors like Getvisibility have recently commented that new regulations, similar to the EU GDPR, will change how companies protect and govern personal information. Consequently, organisations need to have a handle on where their most sensitive data resides, assess their data risk profiles and protecting sensitive files.
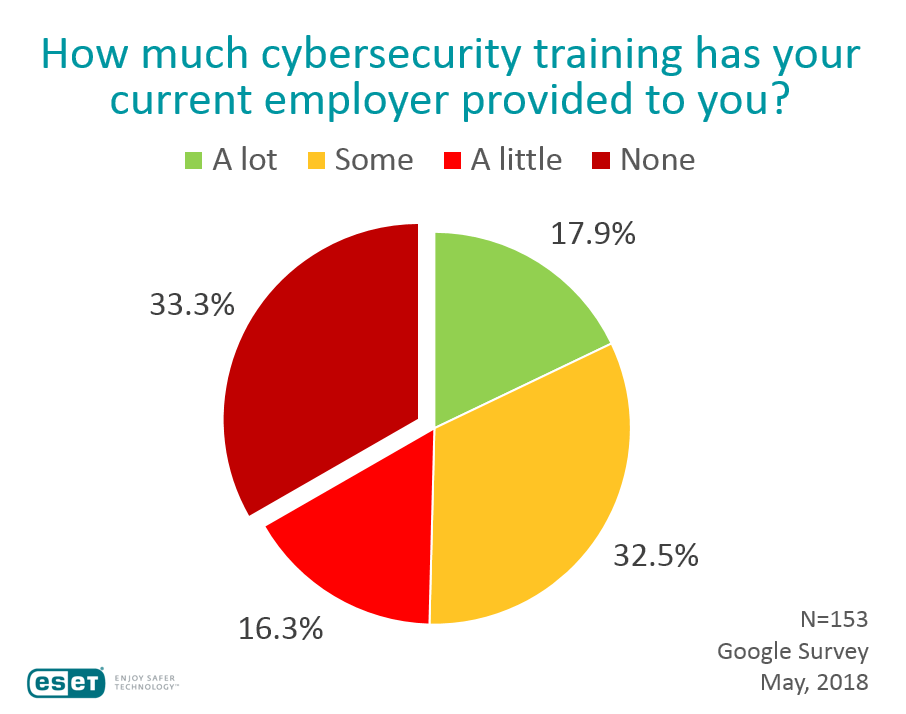
What really surprises us is that as of May 2018, according to an ESET survey, a shocking 33.3% of employees have stated that they have never received cybersecurity awareness training in their organisations. Will this change in 2019?
What about nation-state cyber attacks? We expect nation-state attacks to increase in 2019, particularly targeting critical infrastructure worldwide. Geopolitical tensions and international conflicts will be driving new tactics, techniques and procedures for cyber espionage and nation-state warfare.
As threats diversify and materialise in the wild, companies and governments need to make proper investments in a comprehensive information security strategy that combines the right tools with the right approaches for a better cybersecurity plan. Contact us today and learn more about our 2018 review and how Smarttech247 can help prep your security team for 2019 and beyond.
Contact Us
The data you supply here will not be added to any mailing list or given to any third party providers without further consent. View our Privacy Policy for more information.