Security is complex.

Organizations have to deal with too many security tools, disjointed security operations and limited in-house expertise – all while having to keep up with the constant threat landscape. In order to establish a robust cyber defense, they require transparent security solutions and the expertise to navigate these cyber complexities.
130
is the average number of security tools that enterprise organizations need to manage and maintain, creating complexity, and adding to security costs and risk.
3.5M
open cyber security positions indicating a global skill shortage. Organizations struggle to find the necessary skills and expertise to address complex cybersecurity challenges.
75%
of a security analyst’s time is spent on alert triaging and wasting time on false positives, leading to alert fatigue, burnout and security operations inefficiencies.
As organizations focus on scaling and growing their operations, they also need to elevate their security posture in order to keep up with the expanding attack surface. The modern enterprise today needs a security partner who can bring in the expertise quickly and help them manage their cyber complexities effectively.
Get the support that you need to enhance your cyber defenses and improve your security posture
REDUCE CYBER RISK BY 50% IN THE FIRST 6 MONTHS & INCREASE RESILIENCE
We will add depth to your overall security defense and help you reduce your risk by more than 50% in the first six months
Led by human expertise and powered by the VisionX platform, we provide you with a 24/7 unbeatable Managed Detection & Response (MDR) capability giving you transparent and consolidated security solutions. At Smarttech247, we help you supercharge your security from the get-go and increase your cyber resilience day by day so that you can grow and scale your operations. In every customer engagement, we do all the heavy lifting, from onboarding and go-live to continuous management. We help you respond to incidents and contain them in less than 15 minutes, because in cyber security every minute matters.
SMARTTECH247 IS A TRUSTED PARTNER FOR LEADING GLOBAL ORGANIZATIONS TO KEEP THEM SECURE
…and many more
Respond to threats faster than ever.


Single Platform. Complete Solution.
driving better security outcomes
Unbeatable MDR

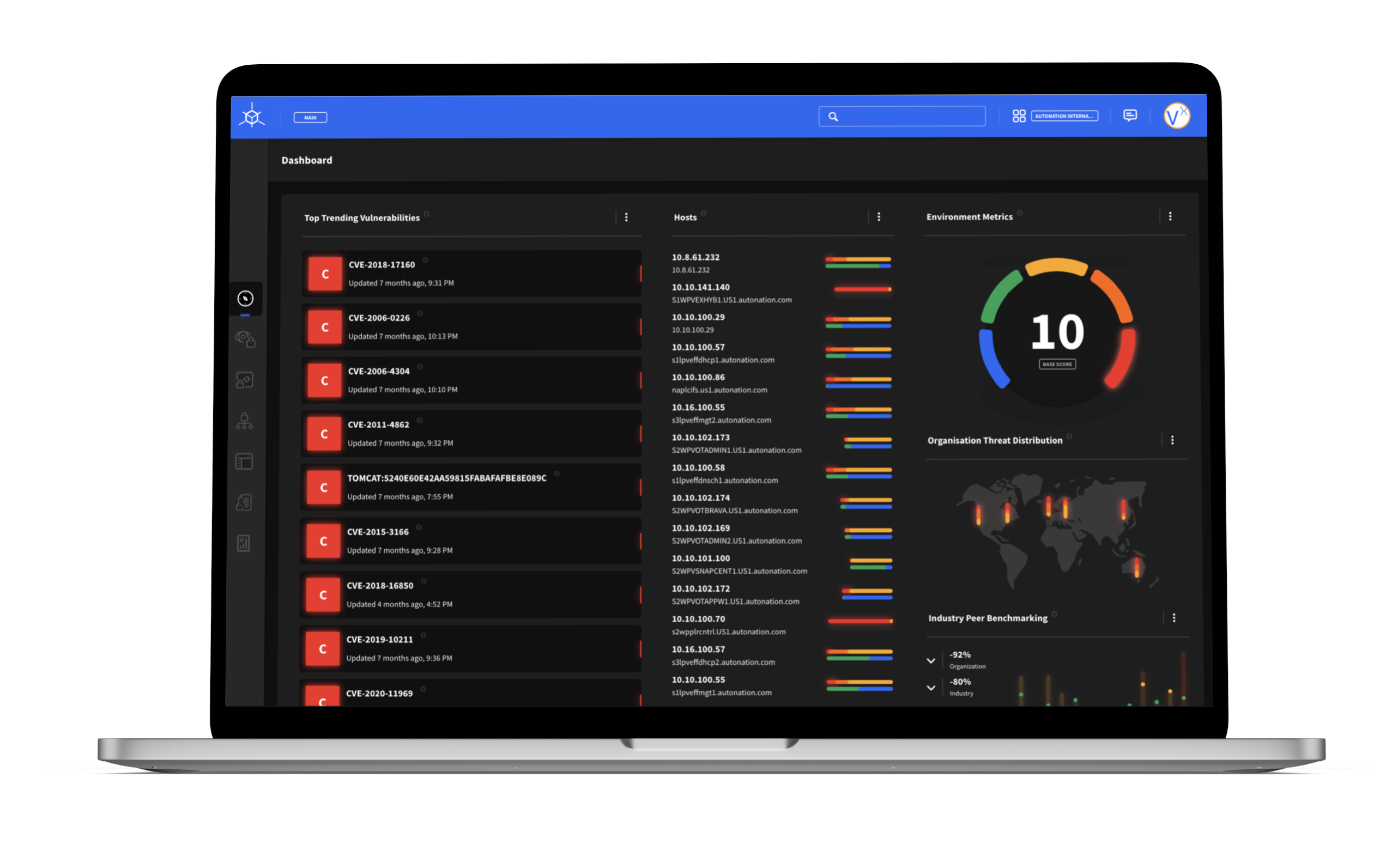
VisionX is our unbeatable MDR platform that consolidates all your security risks under a single solution and provides you with a single pane of glass. A perfect combination of people, process and technology, VisionX plugged with our Security Operations Center intelligence, enables you to detect threats proactively and respond to attacks faster. Our platform sits on top of powerful SIEM & SOAR engines with multiple out-of-the-box integrations to provide you an unbeatable Managed Detection & Response on a 24/7 basis.
<15 min
MEAN TIME TO RESPOND (MTTR)
500+
THREAT CONTAINMENTS
1000+
LOG SOURCE CORELATIONS
Our VisionX Platform offers next gen MDR Capabilities which includes –

24/7 Expert Led Monitoring
Seamless SIEM & SOAR Integrations
Threat Intelligence Correlation
Extended Attack Surface Visibility
PREVENT

Protect your complete attack surface and prevent incidents with 24/7 always-on security monitoring and real-time threat hunting.
DETECT

Detect faster and better with enriched UBA, advanced threat intelligence & 24/7 rapid SOC analyst support & security investigations.
RESPOND

Respond within minutes & isolate threats immediately without disrupting operations. Remediate better with expert support & build resilience
Enhance your cyber defense with the Smarttech247 difference
At Smarttech247, we commit to stand with you and push our limits to keep you secure everyday. Our customers face unique challenges, therefore we build a dedicated and trusted partnership where we listen first to the needs of our customers and customize our solution to suit their specific requirements. We focus on innovation and constantly aim to add value to our customers’ security environment. With our high-touch approach, we build a relationship based on trust and we deliver expertise, excellence and efficiencies.
Chip Regan, VP & CISO, AutoNation
AWARDS & RECOGNITIONS
Elevate and strengthen your MDR

powering
Attack Surface & Exposure Management
Our AI powered threat intelligence and Exposure Management tool, ThreatHub, is a game changing platform that helps your organisation protect your entire attack surface, on a continuous basis. Along with achieving complete visibility of your attack surface, our platform embedded with next-gen machine learning algorithms and applied context also provides your organisation an added layer of monitoring and protection.
powering
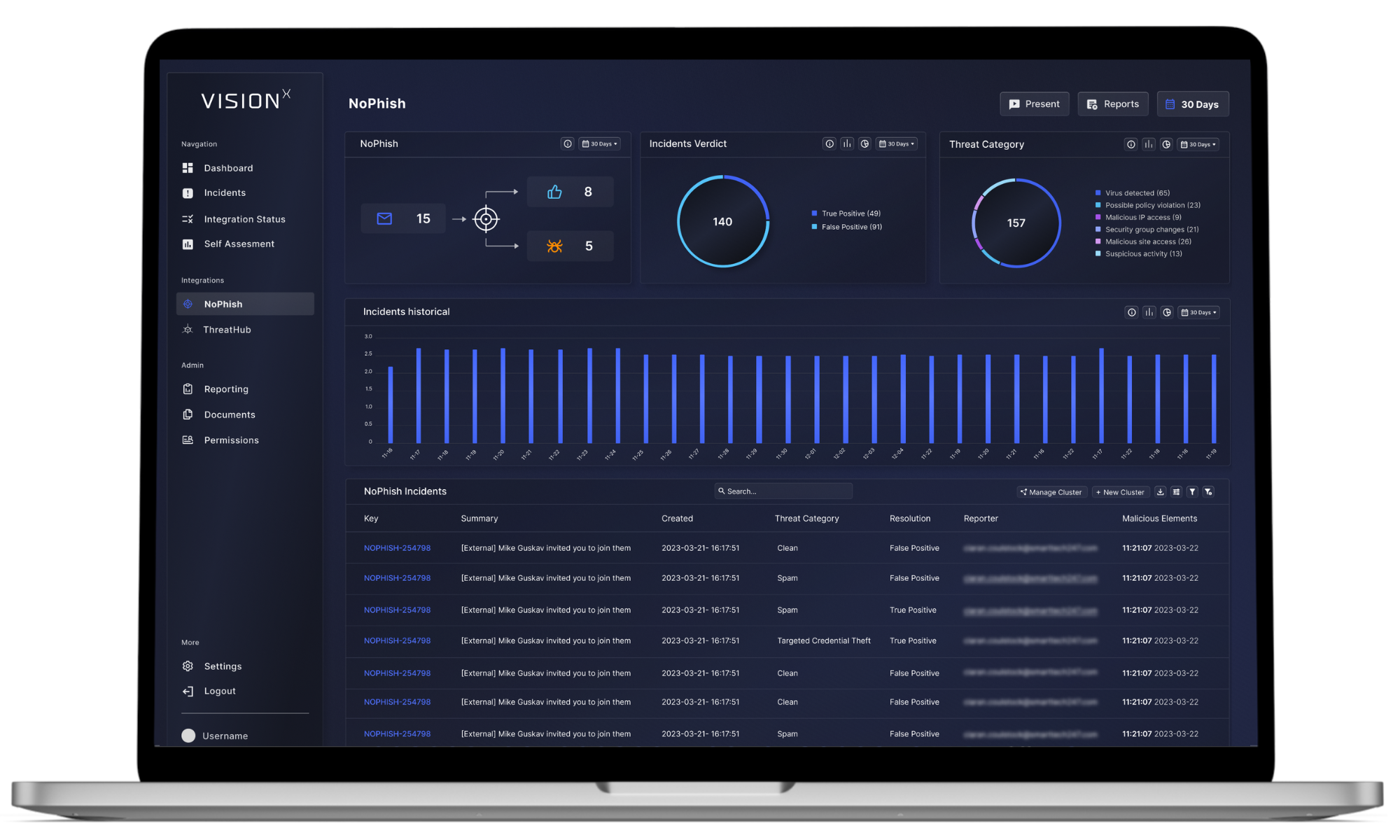
Anti Phishing & Email Security
Our sophisticated anti-phishing software NoPhish helps your organisation safeguard data, information and keep your emails safe at the click of a button. A simple Office 365 app integration, NoPhish can be deployed within minutes without installation of plugins or add-ons on the end point. With NoPhish, we enable you and your users to report a suspicious email with just one click and our expert team does intricate deep dive analysis for you.
What we Do
More Security Services

Cybersecurity Validation
Data and Cloud Securtiy
Threat & Vulnerability Management
Governance, Risk and Compliance
Are you ready to elevate your security with us?
Contact Us
One of our specialists will be in contact with you shortly.